FFT Pipeline Protection: Safeguarding Your Critical Infrastructure with Cutting-Edge Technology
Wiki Article
Why Information and Network Protection Should Be a Top Top Priority for Every Organization
Increasing Cyber Risk Landscape
As organizations significantly count on electronic facilities, the cyber threat landscape has actually expanded significantly a lot more perilous and intricate. A plethora of innovative assault vectors, consisting of ransomware, phishing, and progressed persistent hazards (APTs), posture significant threats to delicate data and functional continuity. Cybercriminals utilize advancing strategies and innovations, making it necessary for organizations to remain vigilant and proactive in their security procedures.The expansion of Internet of Things (IoT) tools has further exacerbated these difficulties, as each attached gadget stands for a potential access point for destructive actors. In addition, the increase of remote work has actually broadened the assault surface area, as employees access corporate networks from numerous locations, often utilizing personal devices that might not stick to rigorous safety methods.
In addition, governing conformity requirements continue to progress, demanding that organizations not just safeguard their information but additionally show their dedication to guarding it. The raising combination of expert system and machine knowing into cyber protection approaches presents both challenges and chances, as these innovations can improve threat detection but may additionally be made use of by foes. In this environment, a flexible and durable security pose is essential for mitigating risks and ensuring business durability.
Financial Ramifications of Data Breaches
Data violations lug significant economic effects for companies, usually resulting in costs that extend far past instant remediation efforts. The preliminary expenditures usually include forensic examinations, system repair work, and the execution of improved safety actions. Nonetheless, the monetary fallout can additionally rise via a range of extra aspects.One major worry is the loss of profits originating from decreased client trust fund. Organizations may experience reduced sales as clients look for more secure options. In addition, the long-lasting impact on brand reputation can result in decreased market share, which is hard to measure yet profoundly affects productivity.
Furthermore, companies may deal with raised prices related to consumer notices, credit scores tracking solutions, and potential settlement insurance claims. The economic concern can additionally encompass potential rises in cybersecurity insurance coverage costs, as insurance providers reassess threat following a violation.
Regulatory Conformity and Legal Risks
Organizations encounter a myriad of regulatory conformity and legal risks following an information breach, which can considerably complicate recuperation initiatives. Various regulations and policies-- such as the General Data Protection Policy (GDPR) in Europe and the Health Insurance Coverage Mobility and Accountability Act (HIPAA) in the USA-- mandate stringent standards for information defense and violation notice. Non-compliance can result in hefty penalties, lawsuits, and reputational damage.
Additionally, companies must browse the facility landscape of state and federal regulations, which can differ substantially. The capacity for class-action legal actions from affected stakeholders or customers better worsens legal challenges. Companies usually encounter analysis from regulatory bodies, which may impose extra penalties for failures in data administration and protection.
In addition to financial repercussions, the lawful ramifications of a data breach may require considerable financial investments in legal advice and conformity resources to handle investigations and removal initiatives. Therefore, recognizing and sticking to relevant laws is not simply a matter of legal commitment; it is crucial for protecting the organization's future and maintaining functional stability in a significantly data-driven environment.
Structure Customer Trust Fund and Loyalty
Frequently, the structure of client trust and loyalty joints on a company's commitment to information safety and privacy. In an era where data breaches and cyber hazards are progressively common, customers are a lot more discerning concerning just how their individual details is handled. Organizations that focus on durable information defense gauges not only protect sensitive info yet likewise promote an atmosphere of count on and openness.When consumers view that a company takes their information security seriously, they are extra most likely to participate in long-lasting connections with that said brand. This trust fund is enhanced via clear interaction regarding data methods, consisting of the kinds of info gathered, how it is used, and the actions taken to secure it (fft perimeter intrusion solutions). Firms that take on a positive method to safety can distinguish themselves in an affordable market, bring about boosted client commitment
Furthermore, companies that show liability and responsiveness in case of a security event can transform possible situations right into opportunities for strengthening customer connections. By constantly prioritizing information protection, organizations not just shield their possessions but likewise grow a devoted customer base that really feels valued and secure in their interactions. By doing this, data safety and security comes to be an important element of brand integrity and customer fulfillment.

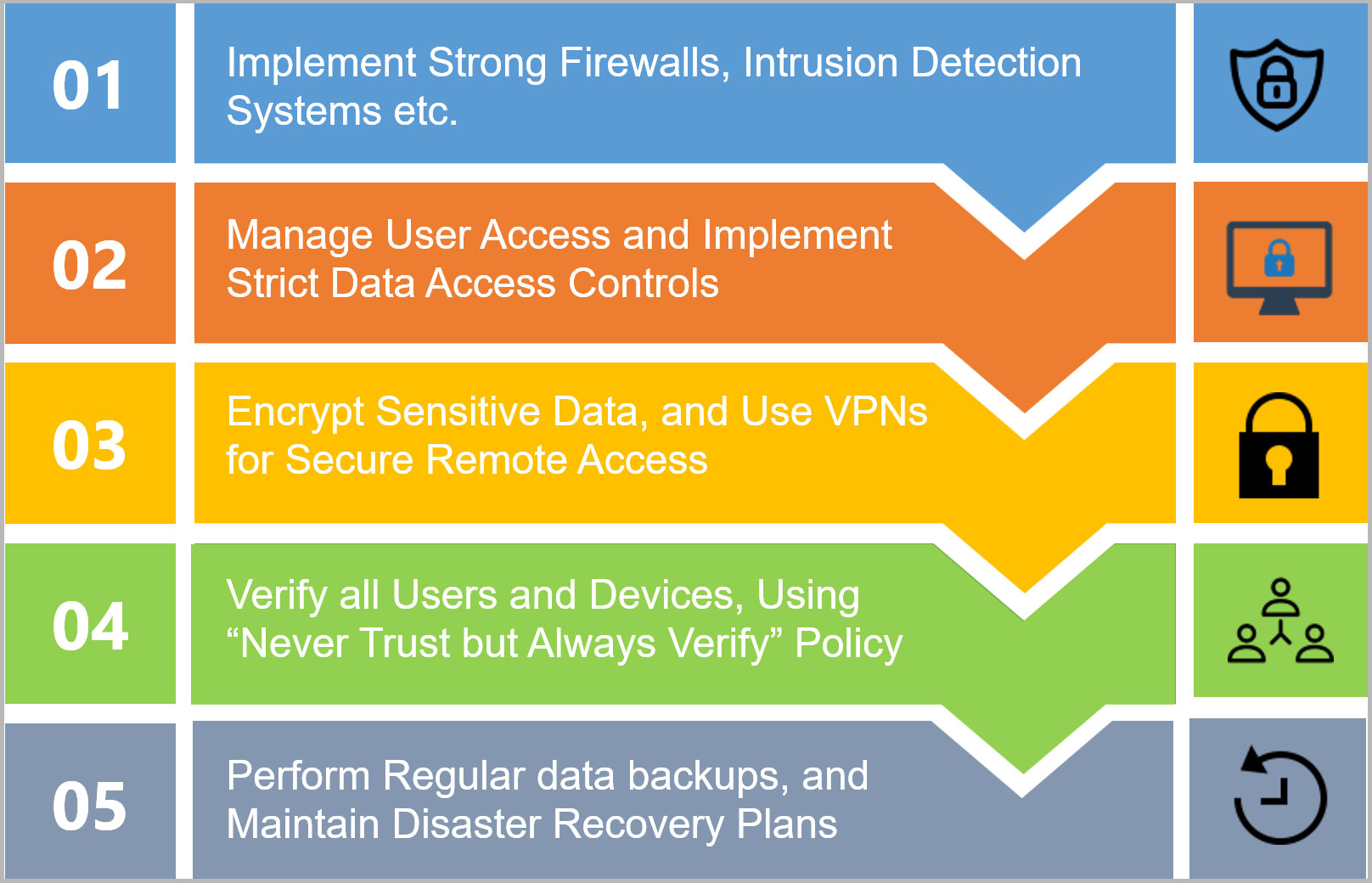
Crucial Strategies for Security
In today's landscape of progressing cyber threats, carrying out necessary strategies for defense is vital for securing sensitive info. Organizations should take on a multi-layered safety approach that includes both technical and human components.First, deploying sophisticated firewall programs and intrusion discovery systems can aid check and block malicious activities. Routine software application updates and spot management are vital in resolving vulnerabilities that can be made use of by enemies.
Second, employee training is crucial. Organizations needs to conduct regular cybersecurity awareness programs, enlightening personnel about phishing rip-offs, social engineering tactics, and secure searching techniques. A well-informed labor force is a powerful line of defense.
Third, information file encryption is crucial for securing delicate info both en route and at rest. fft perimeter intrusion solutions. This makes certain that even data and network security if data is obstructed, it remains hard to reach to unapproved individuals
Conclusion
In final thought, focusing on data and network security is important for companies browsing the progressively complex cyber danger landscape. The economic repercussions of data violations, paired with rigid regulatory compliance needs, underscore the need for robust protection measures.In a period noted by a boosting frequency and refinement of cyber dangers, the essential for companies to focus on data and network protection has actually never ever been more pressing.Regularly, the foundation of consumer count on and commitment joints on a business's dedication to information security and privacy.When consumers regard that a company takes their data safety and security seriously, they are a lot more likely to involve in lasting relationships with that brand name. By constantly focusing on data security, companies not just protect their assets yet also grow a loyal consumer base that feels valued and secure in their interactions.In final thought, prioritizing information and network safety and security is imperative for companies navigating the progressively intricate cyber hazard landscape.
Report this wiki page